Notice: This Wiki is now read only and edits are no longer possible. Please see: https://gitlab.eclipse.org/eclipsefdn/helpdesk/-/wikis/Wiki-shutdown-plan for the plan.
Extensible Protocol RP Website 1.0
{{#eclipseproject:technology.higgins|eclipse_custom_style.css}}
Contents
Version 1.0
- This page describes the Higgins 1.0 Relying Party Solution
- See Extensible Protocol RP Website 1.1 for the version currently under development
Introduction
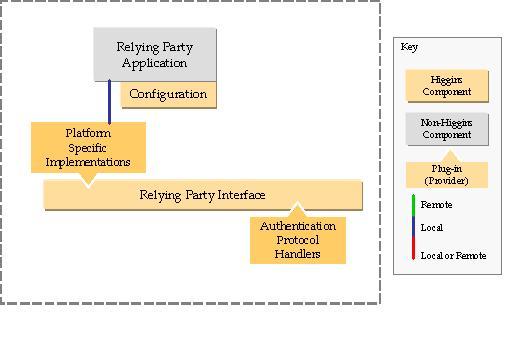
This solution shows an example Relying Party web application that uses the Relying Party Enablement components to provide authentication using an Information Card. The security token that is returned to the Relying Party site is verified and the identity attributes from the token are made available to the web application. This web application is a demo application that shows a photo sharing web site where the user can access more content if they use an Information Card to access protected pages. This solution is built using the servlet container implementation of the Relying Party Interface is intended as an example of how to build a Relying Party application with the Higgins components. The Relying Party Enablement components currently only support authentication using an Information Card but the interface is designed to be extensible and other authentication protocol handlers will be added. This example will evolve to show how to use other forms of authentication and how to build an example that lets the user choose between a number of different authentication mechanisms.
End-User Perspective
A similar application is deployed at https://higgins.eclipse.org/RelyingPartyDemoApp. The end user experience is the same as this example.
Functionality
This application has some protected and unprotected resources. If a user selects the unprotected resoources they will have access to only limited information. The user has access to more data when they use an Information Card to login.
Setup
The user must install the root and intermediary certificates into their browser. There are links for these certificates at the web site for the application. The user must also have an Information Card installed on their system and must have a browser that is enabled with an Identity selector.
Deployer Perspective
Download
Select a build from the higgins downloads and extract the war file from war.zip.
Deploying
Copy the war file to tomcat's webapps folder.
Restart tomcat
Accesshttps://host:port/RelyingPartyDemoApp2in a browser. If you are using a test certificate for tomcat, then you need to install the test certificate in your browser when accessing the URL for the first time.
Note: Vista users needs to run IE7 as Administrator to install Test CA Root Certificate. Otherwise the certificate will be saved in wrong place and IE7 will keep showing certificate error.
Configuration
Copy your SSL keystore file and CA Root file to RelyingPartyDemoApp2/WebContent folder. See Generating a Private Key and a Keystore if you don't have SSL keystore for the tomcat installation.
Update RelyingPartyDemoApp2/WebContent/WEB-INF/web.xml file for the following RP site specific params
- PrivacyUrl to the URL of your privacy statement. This must be a valid URI.
- RootCertUrl to the URL of your CA Root location
Update RelyingPartyDemoApp2/WebContent/icard.properties file for the following Information Card Protocol Handler params
- keystorename to your keystore file name
- keystorepw to your keystore password
- keystoretype to your keystore type
- keystorekeyalias to your keystore alias
Developer Perspective
Architecture
Building
Checkout the following projects to Eclipse workspace from:
https://dev.eclipse.org/svnroot/technology/org.eclipse.higgins/branches/B-1-0-0/plugins
- org.eclipse.higgins.rp.icard
- org.eclipse.higgins.rp.interface
- org.eclipse.higgins.rp.servlet
https://dev.eclipse.org/svnroot/technology/org.eclipse.higgins/branches/B-1-0-0/app
- org.eclipse.higgins.rp.servlet.sample
Also checkout the following project dependencies: (https://dev.eclipse.org/svnroot/technology/org.eclipse.higgins/branches/B-1-0-0/plugins)
- org.eclipse.higgins.configuration.api
- org.eclipse.higgins.configuration.common
- org.eclipse.higgins.configuration.xml
- org.eclipse.higgins.dependencies.redistributable
- org.eclipse.higgins.idas.api
- org.eclipse.higgins.messages
- org.eclipse.higgins.sts.api
- org.eclipse.higgins.sts.base64.apache
- org.eclipse.higgins.sts.common
- org.eclipse.higgins.sts.spi
- org.eclipse.higgins.sts.xmlsecurity.apache
The only error that you see after this step is "Target runtime Apache Tomcat v5.5 is not defined" if you have no Tomcat servers setup in your workspace.