Notice: This Wiki is now read only and edits are no longer possible. Please see: https://gitlab.eclipse.org/eclipsefdn/helpdesk/-/wikis/Wiki-shutdown-plan for the plan.
VIATRA2/Examples/Generating Axis2 Configuration
Outdated page
This page contains obsolete information about the VPM based VIATRA2 and preserved for archive purposes only.
The currently maintained wiki is available at http://wiki.eclipse.org/VIATRA
Contents
This example shows an usage of VIATRA2 for web service configuration generation. It uses an extended UML format which is capable to model services. The transformations generate web service stubs, security configuration and reliability configuration from the model for Axis2 platform.
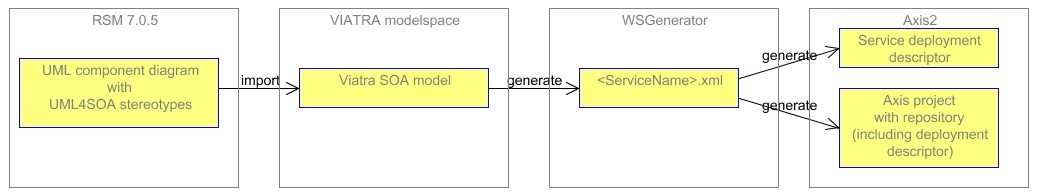
Overview of the process
The starting point is an UML component diagram of the services, where model elements are stereotyped using UML4SOA. The diagram also contains non-functional description of services. The UML model can be imported to Viatra modelspace. Here several transformations can be applied. At the end of the Viatra transformation chain we get XML documents which are the input of a Java program called WSGenerator. The WSGenerator has two operation modes. It can organize directory and file structure for Axis2 archives (aar) and Axis2 repositories based on the XML document generated from Viatra or only generate deployment descriptor files for Axis2 web services (with security and reliability configurations).
UML model with UML4SOA profile
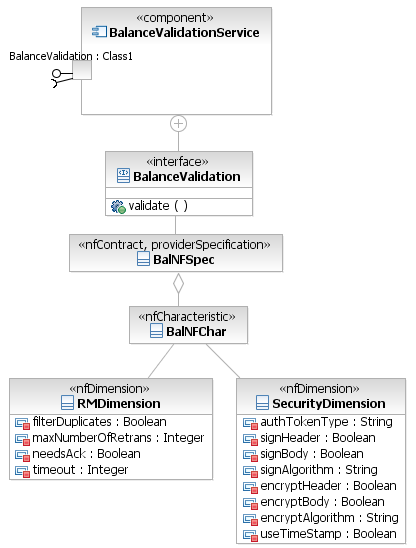
UML component diagram is used for service modelling. The semantics of model elements are the following: Each component represents a service. A service has port with Service stereotype and the port defines required and provided interfaces. The provided interface has ServiceInterface stereotype and gives the operations of the service. Through the parameters of the operation it describes the message types used during communication. An example can be seen on the next figure.
Security and Reliability parameters can be given using the nfContract, nfCharacteristic and nfDimension stereotypes. To define these parameters a class stereotyped as nfContract have to be associated with an Interface stereotyped as ServiceInterface. This class must have another association with a class stereotyped as nfCharacteristic. The nfCharacteristic class has to have an association with two classes stereotyped as nfDimension, one called RMDimension, the other called SecurityDimension. (It is possible to define just one kind of NF dimension.)
SOA model in VIATRA2 and model transformations
VIATRA2 tool of BME has the capability of UML model importing. It can import an UML model from an UML2.1 file to an instance model of its UML metamodel. The UML elements made up this metamodel, for instance Component, Class, Association.
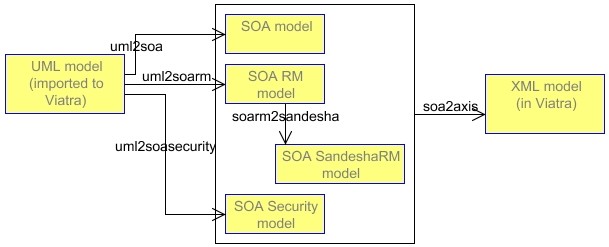
The next figure gives a summary of the used Viatra transformations. The boxes represent model elements, the arrows represents transformations, with the given name.
- UML2SOA transformation: transforms the given UML model into a SOA model.
- UML2SOARM and SOARM2SANDESHA transformations: transforms the reliability parameters of the model to the reliability extension of the SOA model.
- UML2SOASecurity transformation: transforms the security parameters of the model to the security extension of the SOA model.
- SOA2AXIS transformation: creates an XML document (in VIATRA2 modelspace) which will be the input of the WSGenerator application.
WSGenerator application
Generates deployment descriptor, security and reliability configuration and web service stub for Axis2 platform.
The generated deployment descriptor for the above model:
<service name="BalanceValidationServiceService"> <description>BalanceValidationServiceService</description> <messageReceivers> <messageReceiver mep="http://www.w3.org/2004/08/wsdl/in-only" class="org.apache.axis2.rpc.receivers.RPCInOnlyMessageReceiver" /> <messageReceiver mep="http://www.w3.org/2004/08/wsdl/in-out" class="org.apache.axis2.rpc.receivers.RPCMessageReceiver" /> </messageReceivers> <parameter name="ServiceClass"> balancevalidationserviceservice.BalanceValidationServiceService </parameter> <wsp:Policy wsu:Id="SecSpec" xmlns:wsu="http://docs.oasis-open.org/wss/2004/01/oasis-200401-wss-wssecurity-utility-1.0.xsd" xmlns:wsp="http://schemas.xmlsoap.org/ws/2004/09/policy"> <wsp:ExactlyOne> <wsp:All> <sp:AsymmetricBinding xmlns:sp="http://schemas.xmlsoap.org/ws/2005/07/securitypolicy"> <wsp:Policy> <sp:InitiatorToken> <wsp:Policy> <sp:X509Token sp:IncludeToken="http://schemas.xmlsoap.org/ws/2005/07/securitypolicy/IncludeToken/AlwaysToRecipient"> <wsp:Policy> <sp:WssX509V3Token10 /> </wsp:Policy> </sp:X509Token> </wsp:Policy> </sp:InitiatorToken> <sp:RecipientToken> <wsp:Policy> <sp:X509Token sp:IncludeToken="http://schemas.xmlsoap.org/ws/2005/07/securitypolicy/IncludeToken/Never"> <wsp:Policy> <sp:WssX509V3Token10 /> </wsp:Policy> </sp:X509Token> </wsp:Policy> </sp:RecipientToken> <sp:AlgorithmSuite> <wsp:Policy> <sp:TripleDesRsa15 /> </wsp:Policy> </sp:AlgorithmSuite> <sp:Layout> <wsp:Policy> <sp:Strict /> </wsp:Policy> </sp:Layout> <sp:IncludeTimestamp /> <sp:SignBeforeEncrypting /> <sp:OnlySignEntireHeadersAndBody /> </wsp:Policy> </sp:AsymmetricBinding> <sp:Wss10 xmlns:sp="http://schemas.xmlsoap.org/ws/2005/07/securitypolicy"> <wsp:Policy> <sp:MustSupportRefKeyIdentifier /> <sp:MustSupportRefIssuerSerial /> </wsp:Policy> </sp:Wss10> <sp:SignedParts xmlns:sp="http://schemas.xmlsoap.org/ws/2005/07/securitypolicy"> <sp:Body /> </sp:SignedParts> <ramp:RampartConfig xmlns:ramp="http://ws.apache.org/rampart/policy"> <ramp:user>service</ramp:user> <ramp:encryptionUser>client</ramp:encryptionUser> <ramp:passwordCallbackClass> balancevalidationserviceservice.PWCBHandler </ramp:passwordCallbackClass> <ramp:signatureCrypto> <ramp:crypto provider="org.apache.ws.security.components.crypto.Merlin"> <ramp:property name="org.apache.ws.security.crypto.merlin.keystore.type"> JKS </ramp:property> <ramp:property name="org.apache.ws.security.crypto.merlin.file"> service.jks </ramp:property> <ramp:property name="org.apache.ws.security.crypto.merlin.keystore.password"> apache </ramp:property> </ramp:crypto> </ramp:signatureCrypto> <ramp:encryptionCypto> <ramp:crypto provider="org.apache.ws.security.components.crypto.Merlin"> <ramp:property name="org.apache.ws.security.crypto.merlin.keystore.type"> JKS </ramp:property> <ramp:property name="org.apache.ws.security.crypto.merlin.file"> service.jks </ramp:property> <ramp:property name="org.apache.ws.security.crypto.merlin.keystore.password"> apache </ramp:property> </ramp:crypto> </ramp:encryptionCypto> </ramp:RampartConfig> </wsp:All> </wsp:ExactlyOne> </wsp:Policy> <wsp:Policy xmlns:wsp="http://schemas.xmlsoap.org/ws/2004/09/policy" xmlns:wsu="http://docs.oasis-open.org/wss/2004/01/oasis-200401-wss-wssecurity-utility-1.0.xsd" xmlns:sandesha2="http://ws.apache.org/sandesha2/policy" wsu:Id="RMPolicy"> <sandesha2:RMAssertion> <wsp:Policy> <sandesha2:AcknowledgementInterval> 100 </sandesha2:AcknowledgementInterval> <sandesha2:RetransmissionInterval> 10000 </sandesha2:RetransmissionInterval> <!-- '-1' conveys that there is no limit to the max. number of retransmissions.--> <sandesha2:MaximumRetransmissionCount> 3 </sandesha2:MaximumRetransmissionCount> <sandesha2:ExponentialBackoff> false </sandesha2:ExponentialBackoff> <sandesha2:InactivityTimeout> 60 </sandesha2:InactivityTimeout> <sandesha2:InactivityTimeoutMeasure> seconds </sandesha2:InactivityTimeoutMeasure> <!-- Once a sequence has been marked as deleted, or timed out, this is the length of time that the sequence will remain before all sequence state is totally removed --> <sandesha2:SequenceRemovalTimeout> 60 </sandesha2:SequenceRemovalTimeout> <sandesha2:SequenceRemovalTimeoutMeasure> seconds </sandesha2:SequenceRemovalTimeoutMeasure> <sandesha2:InvokeInOrder>true</sandesha2:InvokeInOrder> <!-- These will not be overriden by service level policies --> <sandesha2:MessageTypesToDrop> none </sandesha2:MessageTypesToDrop> <!-- This will not be overriden by service level policies --> <sandesha2:StorageManagers> <sandesha2:InMemoryStorageManager> org.apache.sandesha2.storage.inmemory.InMemoryStorageManager </sandesha2:InMemoryStorageManager> <sandesha2:PermanentStorageManager> org.apache.sandesha2.storage.inmemory.InMemoryStorageManager </sandesha2:PermanentStorageManager> </sandesha2:StorageManagers> <!-- This will not be overriden by service level policies --> <sandesha2:SecurityManager> org.apache.sandesha2.security.dummy.DummySecurityManager </sandesha2:SecurityManager> <sandesha2:ContextManager> org.apache.sandesha2.context.DummyContextManager </sandesha2:ContextManager> <sandesha2:MakeConnection> <sandesha2:Enabled>true</sandesha2:Enabled> <sandesha2:UseRMAnonURI> true </sandesha2:UseRMAnonURI> </sandesha2:MakeConnection> <!-- <sandesha2:UseMessageSerialization>true</sandesha2:UseMessageSerialization> --> <sandesha2:EnforceRM>false</sandesha2:EnforceRM> </wsp:Policy> </sandesha2:RMAssertion> </wsp:Policy> <module ref="sandesha2" /> <module ref="rampart" /> <module ref="addressing" /> </service>
--Sotiwin.gmail.com 17:05, 20 June 2008 (EDT)