Notice: this Wiki will be going read only early in 2024 and edits will no longer be possible. Please see: https://gitlab.eclipse.org/eclipsefdn/helpdesk/-/wikis/Wiki-shutdown-plan for the plan.
Persona Data Model 2.0
The Persona Data Model 2.0 (PDM) is builds on Higgins Data Model 2.0 and a number of other models (aka schemas, vocabularies, ontologies). It used by Personal Data Store 2.0 and will likely be used by future Higgins web services.
Contents
- 1 Introduction
- 2 A graph of Persona nodes
- 3 Persona.owl
- 4 vCard
- 5 FOAF
- 6 WSG84
- 7 SKOS
- 8 event.owl
- 9 mapping.owl
- 10 template.owl
- 11 payment.owl
- 12 icard.owl
- 13 rcard.owl
- 14 app-data.owl
- 15 Restrictions on CDM 2.0 EntityIds
- 16 See Also
Introduction
The Persona Data Model 2.0 is an ontology about people. It is based on the Higgins Data Model 2.0 which is in turn based on Context Data Model 2.0 (aka CDM 2.0). This page provides an informal overview.
A graph of Persona nodes
A person is represented as a graph of p:Persona class Entity nodes (vertices) interconnected by links (edges). Each node represents a different facet of the user (person). Each node is an entity (i.e. a set of attributes & values). These attributes may be simple literals (e.g. the user's first name) or they may be other entities. These latter complex attributes are rendered a as links (edges) to other nodes, but these edges and nodes are not considered part of the graph.
The graph is a logical abstraction. The data behind these nodes may be physically located anywhere on the Internet.
Typically each node in the Persona graph is located in its own Context. The root node lies in a special context (for each user) called the root context.
All of the main persona entities can be reached by traversing links of the following kinds, (although other links may also exist (e.g. p:source, foaf:knows, etc.)):
h:correlationh:relationh:indeterminatep:subCorrelation
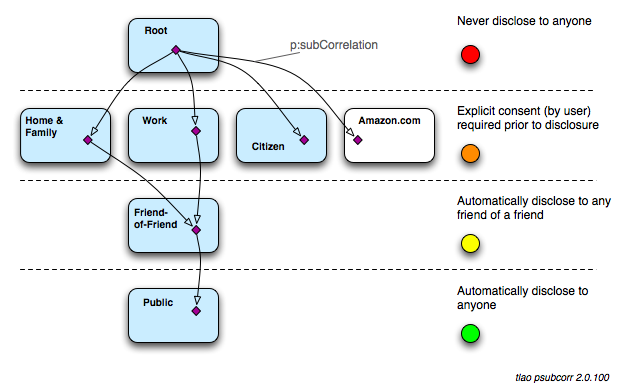
p:subCorrelation and Access Control
PDM adds p:subCorrelation, a specialized (directed) h:correlation. It is a relation between two Personas in different contexts that are asserted to be representing the same person and such that the value entity is used in a broader scope (with generally more relaxed access control policies). The size of the intended "audience" for the value entity is typically larger than the intended audience for the source entity. It is a non-symmetric attribute of an entity. The value of this attribute is another entity.
SubCorrelation allows us to construct a directed graph of entities radiating out from the root node. The root node's attributes are the most privileged information about a person. Below is an example of a directed graph. We have displayed a reasonable "default" access control policy for each "level" (i.e. number of hops from the root) of the graph.
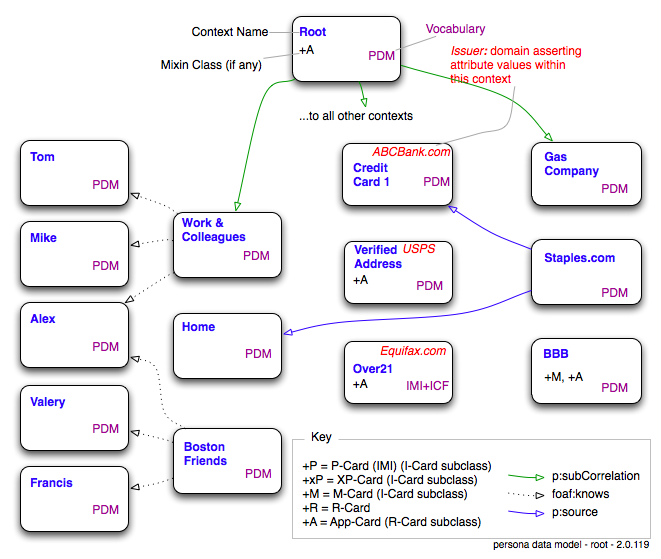
More detailed example graph
A more detailed example graph is shown below. In order to simplify the above diagram we follow a convention whereby the links are drawn between contexts whereas in reality the links are between the main p:persona objects within each of these contexts. Further, these main persona entities may well themselves have complex attributes (i.e. links to other entities). These have also been omitted.
Vocabularies
In the above example all of the contexts except one express their contents using the Persona Data Model (vocabulary) (shown as purple "PDM"s above). The exception is the managed i-card from Equifax which uses attribute (aka claim) URIs defined by the OASIS IMI TC and by the ICF's (Information Card Foundation) schema working group.
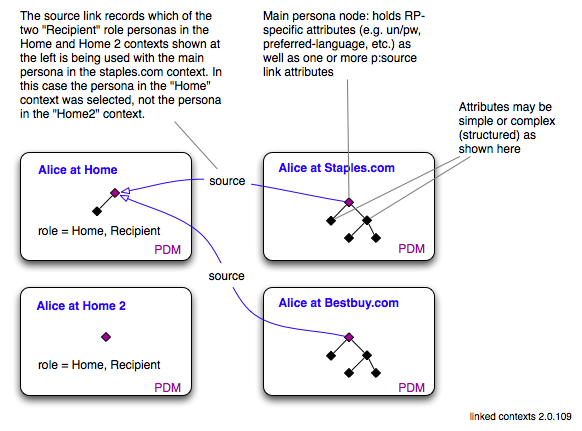
Linked Contexts
A "consuming" persona in one context (e.g. the profile context shown below) may be linked to a "source" persona in another context. This is done by linking the personas with a p:source link (complex-valued attribute). When the persona nodes in two contexts are linked in this way, this is an example of "linked contexts."
These p:source links allow a single consuming persona node to aggregate one or more other persona nodes (usually of differing p:role values) from other contexts. This promotes reuse of personas and contexts and minimizes copying and duplication. For example a "recipient" persona in one context might hold a name, address and phone number that correspond to a physical address, say the person's home. If the user uses this home address in 100 Profile Contexts (e.g. 100 eCommerce websites) each of these 100 context's main personas can have a p:source link to this shared home persona & context, rather than having 100 copies of this persona in each of the 100 contexts.
Every p:source link also has an inverse link p:consumer pointing in the opposite direction. For clarity these "back" links are not shown above. Any persona with more than one "incoming" p:source link (or, said another way more than one outgoing "p:consumer" link) is essentially a "shared" persona. Updating a shared persona has the effect of altering the attribute values that will be returned by the contexts that use a shared persona as a source.
At present these p:source and p:consumer links are used only to link persona entities, not entities in general.
Access Control
Attribute-level Access Control
The rules governing access to attributes in context C1 are defined in an external "control" context C2 where C2 is an instance of Mapping Context. Mapping Contexts also contain other rules unrelated to access control.
@@@@to be completed
Persona-level Access Control and Linked Contexts
In addition to the Attribute-level Access Controls, a user agent has write access to a context if:
- the user agent is the issuer of the context (i.e. it created the context in the first place)
- the persona to be edited is not linked to by "p:source" links from any personas in contexts whose issuer is other than the user agent
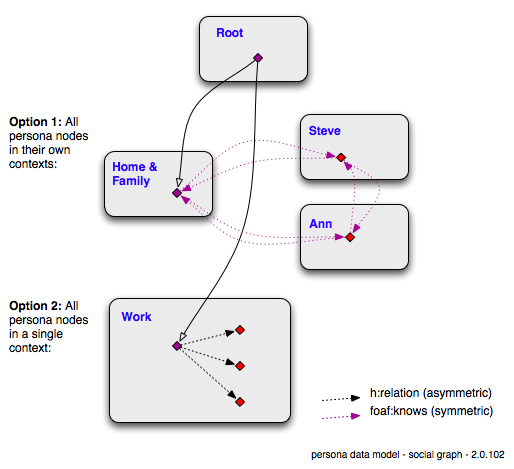
Representing Social Graphs
h:relation
HDM defines a h:relation complex attribute that is used in PDM to link one Persona node to another where each Persona node represents a different person. No symmetry is implied in this thus the statement (A h:relation B) is akin to saying person A "knows of" person B.
Shown below are two social graph examples. One uses foaf:knows links and and (unrelated to this) shows each node in its own context. The other uses h:relation links and (unrelated) shows all persona nodes in a single context. In the Work context we see that the user knows three colleagues but doesn't know how they know one another. In the Home & Family context we see that the user knows two people and that everyone knows one another. The foaf:knows links are shown in both directions although logically this is redundant since foaf:knows is what is a called a symmetric relation.
Nodes that represent the user are shown in purple. Nodes representing a person other than the user are shown in red.
foaf:knows
To indicate that a person A "knows" person B where some level of reciprocated interaction between the parties is implied, we use foaf:knows.
Since foaf:knows is a broader concept than h:relation, foaf:knows is not a sub-attribute of h:relation. Thus if we had the statement "A h:relation B" then we might later add a second statement "A foaf:knows B" to add the stronger, broader (and symmetric) concept of "knowing."
h:indeterminate
HDM also defines h:indeterminate link attribute on node A to indicates that its value(s) may or may not represent the same thing as is represented by A.
Implementation Note
Consumers of the HDM may traverse h:relation, h:correlation and h:indeterminate attribute links and (despite ignoring all other links) traverse the entire graph of h:Persona nodes.
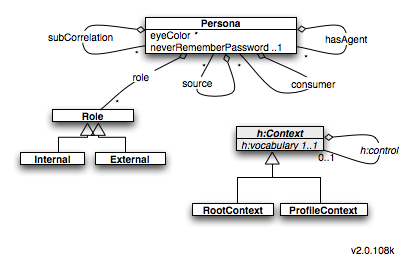
Persona.owl
This is the main vocabulary at the heart of the Persona Data Model 2.0
UML Overview
Classes
Persona
A contextualized aspect (aka facet) of a person.
- subClassOf
h:Person - subClassOf
geo:SpatialThing
- 0..N
subCorrelation - 0..N
hasAgent - 0..N
source
Role
Abstract concept of a role that a Persona plays.
Internal
Roles that a person may play
- subClassOf
Role
Defined instances:
Work: A work-related role.Home: Acting in a personal, non-professional capacity.Buyer: A person who is physically able to receive a bill and pay a bill. This person must be "contactable" to play this role. They must have a v:adr and v:n and optionally other information so that the bill/invoice can be physically delivered to them. Further, they must be able to pay this bill.Recipient: A person who is physically able to receive a letter, parcel or delivery. This person must be "contactable" to play this role. That is, they must have a v:adr and v:n and optionally other information so that the delivery can be physically routed to them.
External
Roles defined by the context of your interaction. E.g. an eCommerce website "imposes" an eCommerce role on you, whereas a gaming site imposes broading a gaming role on you.
- subClassOf
Role
Defined instances:
Ecommerce: A role imposed by eCommerce interactions, e.g. with an eCommerce websiteGaming: A role imposed by gaming-related interactions, e.g. with a gaming website like world of warcraftSocialNetworking: A role imposed by social interactions, e.g. with a social networking site
RootContext
A singleton context that contains the "root" Persona node of the Persona graph.
- subClassOf
h:Context
ProfileContext
- subClassOf
h:Context
A context that stores the following kinds of attributes:
- One or more Persona nodes each with RP-specific attributes
- e.g. united.com frequent flyer number and account balance
-
foaf:OnlineAccountinstance (including p:password)
- Persona nodes that have
p:sourceattributes - Disclosure events
- Events that record what attributes have been disclosed to an RP.
Attributes
eyeColor
- domain:
Persona - value:
xsd:stringoneOf(green, blue, brown)
hasAgent
A person other than the user to whom some authority to act on the user's behalf has been delegated.
- domain:
p:Persona - value:
p:Persona
issuer
In the Higgins Data Model 2.0 all Context attributes are optional. However in the Persona Data Model 2.0 we have this requirement:
- All contexts that are made available by a third party (e.g. the government, a bank, etc.) MUST have a
p:issuerattribute - The attribute value is a URI
- The URI is either the domain name that is the authority behind the attribute assertions or
- The value
http://!self- the user has explicitly asserted entities & attributes in this context - The value
http://!derived- the active client has derived entities & attributes in this context based on observed behavior and/or assertions made by the user in other contexts
neverRememberPassword
Remember whether or not the person wants password managers to capture the password entered into a login form. Only used in Profile Contexts.
- domain:
p:Persona - value:
xsd:boolean
password
The value of the password that a person might enter into a login form. Only used in Profile Contexts
- domain:
foaf:OnlineAccount - value:
xsd:string
role
A role played by a Persona
- domain:
Persona - value:
Role
source
Persona node in another context that describes an aspect (usually a role-specific aspect). Both personas may or may not be representations of the same person.
- domain:
p:Persona - value:
p:Persona
consumer
Inverse of p:source link.
- domain:
p:Persona - value:
p:Persona- consumer
subCorrelation
A relation between two Personas in different contexts that are asserted to be representing the same person and such that the value entity is used in a broader scope (with generally more relaxed access control policies). The size of the intended "audience" for the value entity is larger than the intended audience for the source entity.
- domain:
Persona - value:
Persona
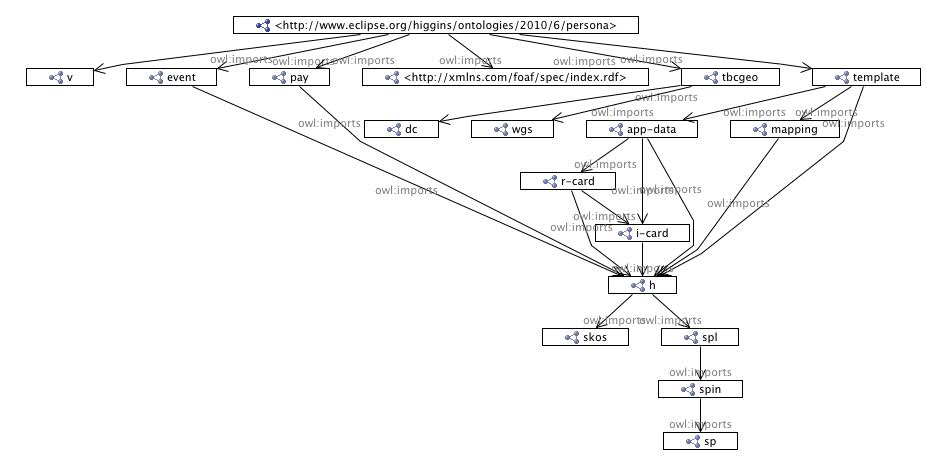
Vocabularies Imported by persona.owl
Higgins-Defined
- event: event types. Most recently published. Svn source: event.owl
- pay: payment methods. Most recently published. Svn source: payment.owl
- app-data: app-data context definition. Most recently published. Svn source: app-data.owl
- r-card: relationship card. Most recently published. Svn source: rcard.owl. See also R-Card.
- i-card: information card represented in OWL. Most recently published. Svn source: icard.owl. See also I-Card.
- mapping: vocabulary mapping rules. Most recently published. Svn source: mapping.owl
- template: template context. Most recently published. Svn source: template.owl
- h: Higgins data model. Most recently published. Svn source: higgins.owl. See also: Higgins Data Model 2.0.
External
- v = vCard
- geo = WGS84 Geo Positioning
- foaf = Friend Of A Friend ontology
- skos = SKOS ontology
- spl = SPL, spin = SPIN, sp = SP
- dc = Dublin Core
- owl = OWL 2, RDFS, RDF
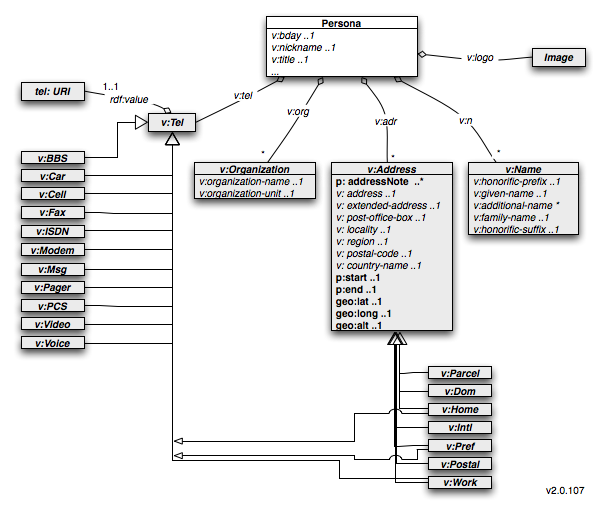
vCard
Persona imports vCard, uses most of it as is, but with a few tweaks described below.
UML Overview
We show below the aspect of PDM that builds on the vCard ontology. The heart of the PDM model is the p:Persona class. Concepts from vCard are shown in italics. Item in non-italics are defined in persona.owl discussed further on.
Classes
Note: Additional attributes from persona.owl are shown in bold below.
v:Address
- p:addressNote *
- p:start ..1
- p:end ..1
- v:address ..1
- v:extended-address ..1
- v:post-office-box ..1
- v:locality ..1
- v:region ..1
- v:postal-code ..1
- v:country-name ..1
v:Name
- v:honorific-prefix ..1
- v:given-name ..1
- v:additional-name *
- v:family-name ..1
- v:honorific-suffix ..1
v:Organization
- v:organization-name ..1
- v:organization-unit ..1
Other attributes
- v:logo
- v:tel
Other vCard classes
- v:Label (disjoint with v:Tel) - not used (don't yet understand what it is)
- v:Tel - not used; we use foaf:phone instead
Attributes
The following attributes are not used:
- v:street-address - we use the more granular p:street, p:houseName, p:houseNumber, p:apartment instead
- v:category
- v:class
- v:email - we use foaf:mbox instead
- v:fn
- v:agent - we use hasAgent instead
- v:geo - we use geo:location instead
- v:key
- v:mailer - not sure what this is
- v:photo - we use foaf:thumbnail instead
- v:prodid
- v:rev
- v:sort-string
- v:sound
- v:tz - not sure syntax of range/value
- v:uid - we use entityId instead
- v:url - we use foaf:page (and sub-attributes) instead
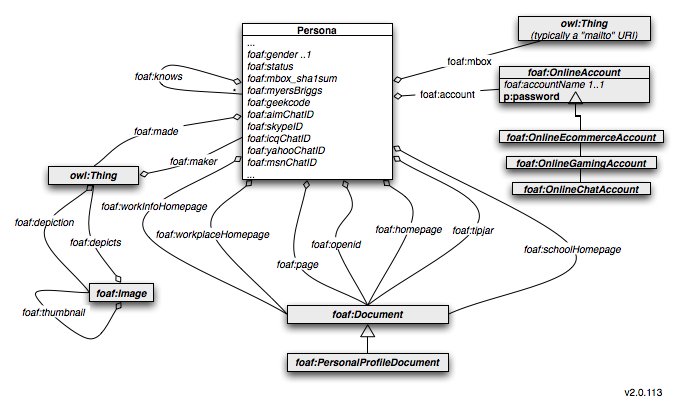
FOAF
Persona.owl imports FOAF and uses some of the classes and attributes it defines.
UML Overview
We show below the aspect of PDM that builds on the FOAF ontology:
Classes
- foaf:OnlineAccount
- foaf:OnlineEcommerceAccount
- foaf:OnlineGamingAccount
- foaf:OnlineChatAccount
- foaf:Document
- foaf:PersonalProfileDocument
- foaf:Image
Attributes
- foaf:account
- foaf:accountName
- foaf:status
- foaf:myersBriggs
- foaf:geekcode
- foaf:geekcode
- foaf:aimChatID
- foaf:skypeId
- foaf:skypID
- foaf icqChatID
- foaf:yahooID
- foaf:msnChatID
- foaf:made
- foaf:maker
- foaf:mbox
- foaf:mbox_sha1sum
- foaf:depicts
- foaf:depiction
- foaf:knows
- foaf:gender
- foaf:thumbnail
- foaf:page
- foaf:homepage
- foaf:weblog
- foaf:openid
- foaf:tipjar
- foaf:schoolHomepage
- foaf:workplaceHomepage
- foaf:workInfoHomepage
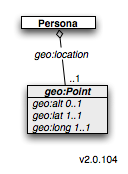
WSG84
Persona.owl imports WGS84 and uses some of its classes and attributes.
UML Overview
We show below the aspect of PDM that builds on the geospatial ontology:
Classes
- geo:Point
- geo:SpatialThing (a p:Persona is a subclass of geo:SpatialThing)
Attributes
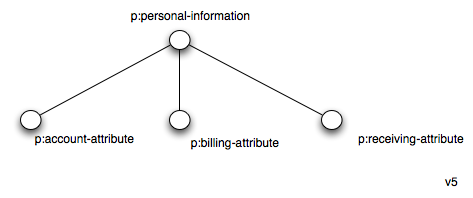
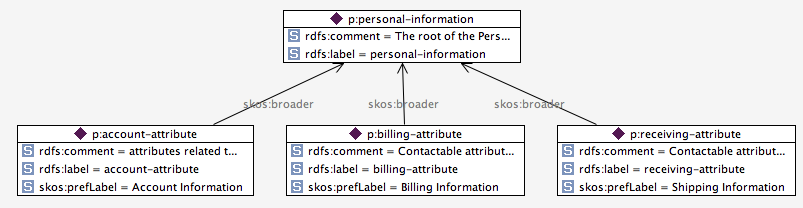
SKOS
Persona.owl imports the SKOS ontology and uses a few of its classes and attributes.
Classes
- skos:Concept
Attributes
- skos:concept
- skos:broader
Concept Scheme (instance)
Persona.owl includes a concept hierarchy defined using SKOS. This hierarchy can be used by visual editors (e.g. a persona editor) to help organize the UI. Attributes defined in persona.owl include skos:concept annotations to indicate the category of concept the attribute belongs to.
Which is represented as:
Note: see Higgins Data Model 2.0 for more information on concept schemes.
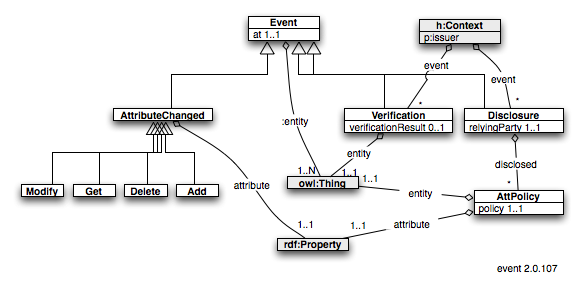
event.owl
A vocabulary to describe events that happen at a specific date and time and that affect either a specific attribute of an entity or all attributes of that entity. Event types include CRUD operations, verification events and disclosure events.
UML Overview
Classes
Event
Change event. Abstract superclass. Subclasses describes changes to an attribute "attribute" of some entity "entity" that happened at dateTime "at"
- 1..1 at
- 1..N entity
AttPolicy
An association of an attribute of some entity with a disclosure policy
- 1..1 policy
- 1..1 attribute
- 1..1 entity
AttributeChanged
A class of events wherein a single attribute is changed
- subClassOf Event
- 1..1 attribute
- 1..1 entity
Add
New value "value"(s) was/were added to attribute "attribute" of entity "entity" at dateTime "at"
- subClassOf AttributeChanged
- 1..N value - "new" value(s)
Delete
One, more or all values of attribute "attribute" of entity "entity" was deleted at dateTime "at". Values to be deleted are specified by one or more "oldValue"(s). If all values of attribute "attribute" are to be deleted then the oldValue (attribute) is omitted.
- subClassOf AttributeChanged
- 1..N oldValue
Get
One or more values of attribute "attribute" of entity "entity" was read at dateTime "at"
- subClassOf AttributeChanged
Modify
The attribute "attribute" of entity "entity" was modified at datetime "at". The value "oldValue" was replaced with value(s) "newValue"
- subClassOf AttributeChanged
- 1..1 oldValue
- 1..N value
Disclosure
A disclosure of attributes to an external party (e.g. an RP website). Each "entity" points to a context object (h:Context instance)
- subClassOf Event
- 1..1 relyingParty
- 1..N disclosed
Verification
Verification event performed by the p:issuer of this context. If event:attribute is not present then event:entity(ies) in their entirety have been verified. Else if event:attribute is present then just the attribute mentioned has been verified.
- subClassOf Event
- 1..1 entity
- 0..1 verificationResult
Attributes
at
When this event happened
- domain: Event
- value: dateTime
attribute
- value: an attribute
disclosed
The attribute that has been disclosed/blocked
- domain: Disclosure
- value: AttPolicy
entity
The entity that has been verified
- domain: Event
- value: an entity
event
An event that happened. Used to associate event(s) with some object to which it relates (often an h:Context)
- value: Verification
oldValue
Old value of an attribute
- domain: Delete, Modify
- value: entity or literal
policy
- domain: AttPolicy
- value: string value one of {"allow", "block"}
relyingParty
- domain: Disclosure
- value: xsd:anyURI
value
New value(s)
- domain: Add, Modify
- value: entity or literal
verificationResult
Result of verification New value(s)
- domain: Verification
- value: one of {"false" , "indeterminate" , "true"}
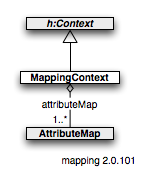
mapping.owl
A context holding vocabulary mapping rules.
UML Overview
Classes
@@@TODO
Attributes
@@@TODO
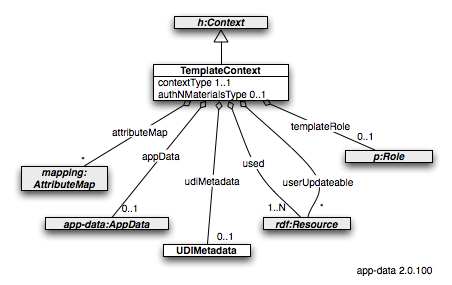
template.owl
Vocabulary that describes a Template Context. Contains several kinds of "control" information necessary to instantiate and control (e.g. provide access control policies) for regular context instances.
UML Overview
Classes
TemplateContext
Template context. Contains several kinds of "control" information necessary to instantiate and control (e.g. provide access control policies) for regular context instances.
- 0..1
app-data:appData- provides a "template" for the AppData object within a dynamically created AppDataContext - 1..1
authNMaterials- part of the metadata necessary to dynamically generate an XRDS service endpoint block within an XRDS - 1..1
contextType- part of the metadata necessary to dynamically generate an XRDS service endpoint block within an XRDS - 0..N
mapping:attributeMap- if present provides RP-to-PDM (and back) vocabulary transformation rules - 1..1
templateRole- the default role that persona nodes should inherit when dynamically created with contexts controlled by on this template - 0..1
udiMetadata- part of the metadata necessary to dynamically generate an XRDS service endpoint block within an XRDS - 1..N
used- a list of 1..N attributes that are actually used in contexts controlled by this template context - 0..N
userUpdateable- a list of 0..N attributes that the user (or user agent) is allowed to modify, delete or add to
UDIMetadata
A set of attribute/values that, taken together, are considered the "Metadata" for the XRDS service endpoint. See http://www.azigo.com/udi/udi-resolution.html#anchor3 for an example.
Attributes
authNMaterialsType
Type of authentication materials required to open this context.
- domain: TemplateContext
- value: string, one of {"urn:udi:authnmaterials:1.0:usernamePassword"}
contextType
The type of context endpoint to instantiate from this template. This corresponds to the value of the <Type> element in XRDS resolution (see http://www.azigo.com/udi/udi-resolution.html).
- domain: TemplateContext
- value: string, one of {"$context$sparql" , "$context$xdi"}
templateRole
The type of context endpoint to instantiate from this template. This corresponds to the value of the <Type> element in XRDS resolution (see http://www.azigo.com/udi/udi-resolution.html).
- domain: TemplateContext
- value: persona:Role
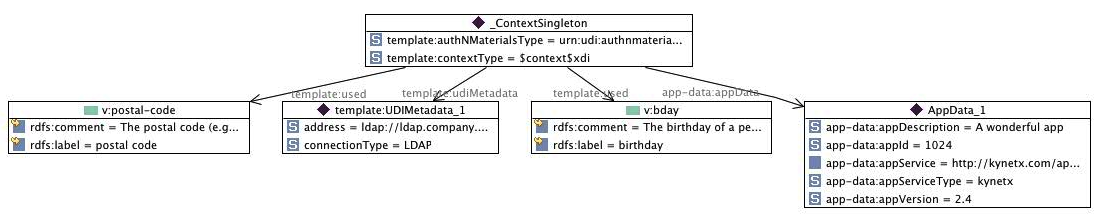
Example
Here is a sample TemplateContext. It contains all of the metadata necessary to dynamically create the UDI service endpoint shown in this sample XRDS discovery document.
:AppData_1
rdf:type app-data:AppData ;
app-data:appDescription
"A wonderful app"^^xsd:string ;
app-data:appId "1024"^^xsd:string ;
app-data:appService "http://kynetx.com/appServer"^^xsd:anyURI ;
app-data:appServiceType
"kynetx"^^xsd:string ;
app-data:appVersion "2.4"^^xsd:string .
:_ContextSingleton
rdf:type template:TemplateContext ;
template:authNMaterialsType
"urn:udi:authnmaterials:1.0:usernamePassword"^^xsd:string ;
template:contextType
"$context$xdi"^^xsd:string ;
template:udiMetadata UDIMetadata_1 ;
template:used <http://www.w3.org/2006/vcard/ns#bday> , <http://www.w3.org/2006/vcard/ns#postal-code> ;
template:userUpdateable
<http://www.w3.org/2006/vcard/ns#bday> ;
app-data:appData :AppData_1 ;
higgins:vocabulary <http://www.eclipse.org/higgins/ontologies/2010/6/persona> .
:address
rdf:type owl:DatatypeProperty ;
rdfs:domain template:UDIMetadata ;
rdfs:range xsd:string .
:connectionType
rdf:type owl:DatatypeProperty ;
rdfs:domain template:UDIMetadata ;
rdfs:range xsd:string .
:UDIMetadata_1
rdf:type template:UDIMetadata ;
:address "ldap://ldap.company.net:389"^^xsd:string ;
:connectionType "LDAP"^^xsd:string .
Or visually:
Notes:
- userUpdateable attribute not shown above
- vocabulary attribute not shown above
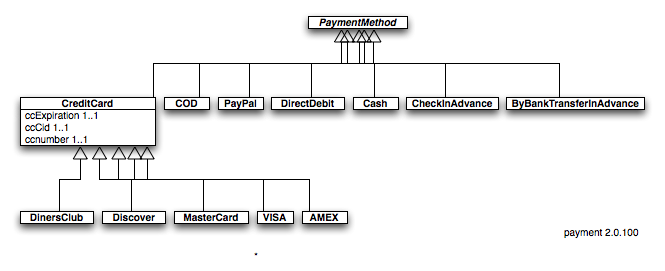
payment.owl
UML Overview
Classes
PaymentMethod
Method of payment including credit cards, paypal, etc.
ByBankTransferInAdvance, Cash, CheckInAdvance, COD
- subclassOf:
PaymentMethod
CreditCard
- subclassOf:
PaymentMethod - 1..1
ccCid - 1..1
ccExpiration - 1..1
ccNumber
AMEX, DinersClub, Discover, MasterCard, VISA, DirectDebit, PayPal
- subclassOf:
CreditCard
Attributes
ccCid
- domain:
CreditCard - value:
xsd:string
ccExpiration
- domain:
CreditCard - value:
xsd:date
ccNumber
- domain:
CreditCard - value:
xsd:string
paymentMethod
- domain:
Persona - value:
PaymentMethod
icard.owl
Information Card (aka i-card) technology is defined by the OASIS IMI TC. It is a standard way to represent a person's digital identities using a card metaphor, XML card formats, and associated SOAP and HTTP network protocols. See also I-Card.
Before we introduce the I-Card classes, remember that in CDM multiple inheritance is allowed: any single entity may be a member of multiple classes simultaneously.
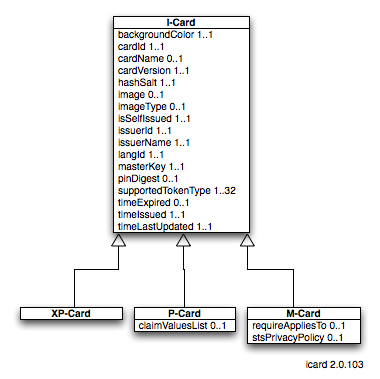
UML Overview
Classes
I-Card
Abstract class
- subclassOf:
h:Context. - 1..1
cardId (xsd:string)- a unique identifier for the card - 1..1
image- an image bitmap for the background of the card when it is displayed - ... others.
P-Card
An OASIS IMI Personal card
- subclassOf:
I-Card
M-Card
An OASIS IMI Managed card
- subclassOf:
I-Card
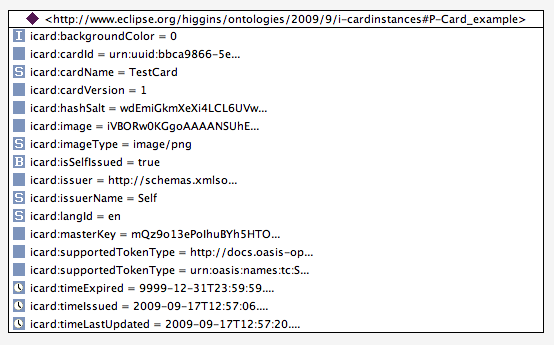
P-Card Attributes
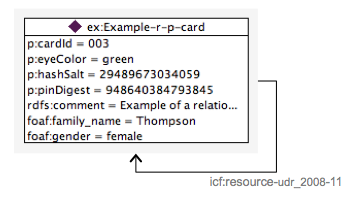
The attributes that define a personal card are taken directly from the OASIS IMI specification. An example p-card is shown here:
ERRATA: context object entity id should be _ContextSingleton
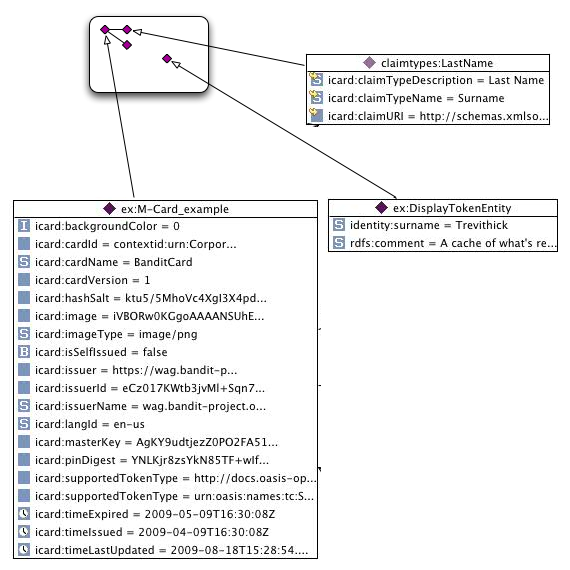
M-Card Attributes
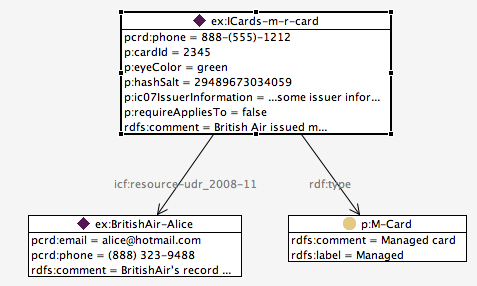
Shown below is an example of an instance of an m-card. For simplicity this m-card has only a single supported claim, "LastName". The entity shown in the center of the card is a cache of what is returned by the STS in response to a request for a display token.
Note: There is an error in the above diagram the DisplayTokenEntity should have been modeled in the Persona data model (thus identity:surname would have been transformed into its equivalent in PDM.
Card Axioms
- For any M-Card: The value of any of the above "supported" claims attributes is considered to be a cache of the most recent value of these claims as fetched from the m-card's STS
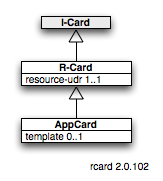
rcard.owl
Vocabulary to describe R-Cards (including App-Cards).
UML Overview
Classes
R-Card
A Higgins relationship card (R-Card), which is essentially a profile of an IMI managed or personal i-card.
- subClassOf
i-card:I-Card - 1..1
resource-udr
AppCard
An App-Card is an r-card that supports a Javascript app. It's resource-udr is a reference to a target entity in an AppData context (see app-data.owl). This resource-udr's target entity and its surrounding context are described by the app-data ontology.
- subClassOf: R-Card
- 0..1 template (URL) - a link to an external "template" context (See TemplateContext class in template.owl vocabulary)
Attributes
resource-udr
Representation of the http://schemas.informationcard.net/@ics/resource-udr/2009-03 claim type.
- domain:
R-Card - value:
xsd:anyURI- UDI resource reference
template
A serialization in RDF n3 notation of a TemplateContext (see the section on the "template.owl" vocabulary)
- domain:
AppCard - value:
xsd:anyURI
Personal R-Card Example
From a structural point of view, the presence of the resource-udr claim on a P-Card or an M-Card makes it be considered an R-Card. Here is an example of a personal R-Card:
ERRATA: the above image is incorrect for PDM 2.0. As above the card is a context. The entity (in this case referenced by the value of the resource_udr claim) would be a free standing Persona entity (as above) and described in the PDM 1.1 model. Also icf: prefix should be removed along with ...2008... suffix. Also entityid of context object should be _ContextSingleton
Managed R-Card
The final type of card is the managed r-card. The presence of the resource-udr claim makes an ordinary M-Card into an R-Card. Here is an example of a managed R-Card:
ERRATA: The image above needs to be replaced. Card entityid should be _ContextSingleton
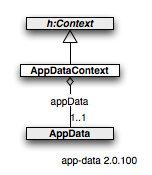
app-data.owl
Provides the classes and attributes to represent the "target" entity pointed to by an app-card as well as the app metadata and parameters for the app itself
UML Overview
Classes
AppDataContext
A kind of context holding an AppData instance as well as the entity referenced by the resource-udr of an AppCard
- subClassOf: h:Context
- 1..1
appData
AppData
The information about an app. This information is pointed to by a appData attribute held by the context holding the target of an app-card's resource-udr.
- 1..1
appId - 1..1
description - 1..1
version - 1..1
eventHandlerURL - 1..1
adminURL - 1..1
serviceType- the type of service from which the Javascript is fetched - 1..1
service- the Javascript service URL - 0..1
params - 0..N
hbxFunctionsEnabled - 0..N
sites - 0..N
entityParam
AppParams
An AppParams instance is the value of an AppCard's params attribute. It is a set of attributes and values used to initialize the app. Note: these attribute/values are combined with those derived from the AppCard's entityParam.
AppDataContext Attributes
appData
The information about an app. This information is pointed to by the context holding the target of an app-card's resource-udr attribute.
- domain:
AppDataContext - value:
AppData
AppData Attributes
appId
Uniquely identifies the app within the "developerId" (i.e. the card issuer) namespace. In other words the combination of the devID and the appId is globally unique. When using Kynetx KNS this is the ruleID with special constraint that this ruleID is globally unique.
- domain:
AppData - value: string
description
A human readable description of the app. Note: If appServer == http(s)://init.kobj.net, then the KNS "describe" API can be used by a context provider implementation to provide this attribute value.
- domain:
AppData - value: string
entityParam
The name of an attribute (e.g. p:postal-code) of the "target" entity of the app-card. The value of this named attribute of the target entity is used as a parameter to the app-card's app.
- domain:
AppData - value: URI
adminURL
The URL of a webapp to load into an active client's "dashboard" (admin) UI.
- domain:
AppData - value: xsd:anyURI
entityParam
The value is the (URI) name of an attribute on the AppCard's target entity. This referenced attribute and its value should be used to initialize the app.
- domain:
AppData - value: URI name of an attribute
params
A set of attributes used to initialize the app.
- domain:
AppData - value: AppParams
service
The URI giving the endpoint from which the Javascript should be fetched.
- domain:
AppData - value: URI
serviceType
If value is "kynetx" then the browser extension that will inject the Javascript for this app-card should construct a Kynetx-compatible <script> block and call an initialization URL based on the value of the appService attribute.
- domain:
AppData - value: string whose value is one of ("kynetx", "higgins").
sites
This is not a list of specific URIs, it is a list of strings to match in the domain name part of a URI. So urn:google would fire on maps.google.com, www.google.com, www.googleismyfavoritesite.com. For Kynetx-powered cards (i.e. if appServer = http[s]://init.kobj.net"), the values of this attribute should be dynamically fetched using the 'dispatch' method at URL: [1]<appId>.
- domain:
AppData - value: string
version
A human readable version of the app. Note: If appServer == http(s)://init.kobj.net, then the Kynetx KNS "describe" API can be used by a context Provider implementation to provide this attribute value.
- domain:
AppData - value: string
Attributes of a Persona within the context
enabledSites
The URLs of sites that the user has enabled the card to run on. Note that this augments the appSites value provided by the card developer which indicates the set of sites the app was designed to run on.
- domain is the target entity to which the underlying r-card's resource-udr points.
- value: boolean
disabledSites
The URLs of sites that the user has disabled the card from running on.
- domain is the target entity to which the underlying r-card's resource-udr points.
- value: xsd:anyURI
appEnabled
- domain is the target entity to which the underlying r-card's resource-udr points. If true the Javascript of this card is enabled to run.
- value: xsd:anyURI
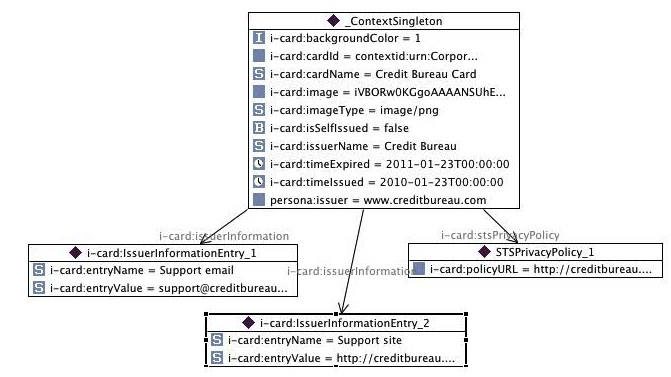
Example AppCard and AppData
Note: Not shown is a r-card:resource-udr link from the AppCard in the upper diagram to the Persona_1 entity in the lower diagram.
AppCard
Example of an AppCard context:
Note: missing from the above diagram is the list of supported claims. This list would include the ICF's resource-udr claim type.
AppData
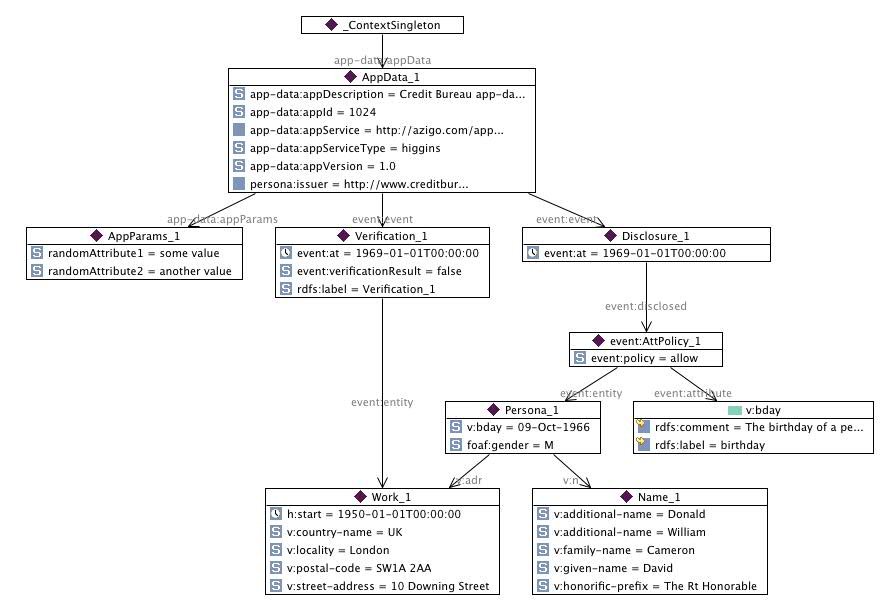
Example of an AppData context:
Shown above is an example AppDataContext (shown as _ContextSingleton above) with its required AppData object. Also within this context is an entity, Persona_1.
Notes:
- Of particular interest is the app-card:params attribute whose value is the AppParams_1 object. The AppParams_1 in turn has two app initialization attributes, randomAttribute1 and 2.
- Since "appEnabled" = true attribute/value is not present on Persona_1 its value is assumed to be false and the card is thus disabled at present.
- The above also shows an example of a event:Verification that happened in 1969. Presumably the entire contents of the context were shared with the credit bureau and the Work_1 address was attempted to be verified with a result of "failed."
- The above also shows an example of an event:Disclosure that says that the "v:bday" attribute of the Persona_1 entity has a policy that says that the user "allow"s its disclosure to http://amazon.com.
Restrictions on CDM 2.0 EntityIds
The PDM 2.0 uses a restricted set of the full capabilities of CDM 2.0. The restriction is in the area of EntityIds. PDM 2.0 adds the following constraints:
All entities:
- All entityIds MUST be URIs
- All entityId values MUST be Linked Data URIs or XRI 2.0 URIs
- All entityIds within a given context MUST be either (a) relative to a "base" URI of the context or (b) absolute
- Whether or not an entityID is relative or absolute MUST be able to be determined by inspection of its syntax
- Absolute entityIds MAY be globally resolvable
- Globally resolvable entityIds resolve to an entity (resource description) within exactly one context
Context objects:
- The entityId of the context object singleton is "_ContextSingleton"
See Also
- Persona Attribute List - a list of all of the attribute concepts that can be represented in PDM
- [2] - a developer summary of AppCard implementation issues
Use cases: